How To Hack Any Game On Your Android Smartphone
By hacking android game you can unlock all the levels, use any resource according to your wish and lots more. Proceed with the method shown below to hack any game on your Android. But sometimes while playing our favorite game we get short on our resources that are needed to play that game, like power, weapons or lives etc. That consequence really becomes bothersome, so to overcome this we are here with the trick How To Hack Any Game On Android.
oday millions of character are using the android phone. Now an Android device enhances significant part of our life. Everyone loves to play games on their android device. There are lots of cool games that are today available on your Android device in Google Play Store.
How To Hack Any Game On Android 2018
Now it's time to hack into the game and use any resources that you want to play at any level of the game. The method is really working and will let you alter the game according to your wish. Just proceed with simple steps below.
Steps To Hack Any Game On Android
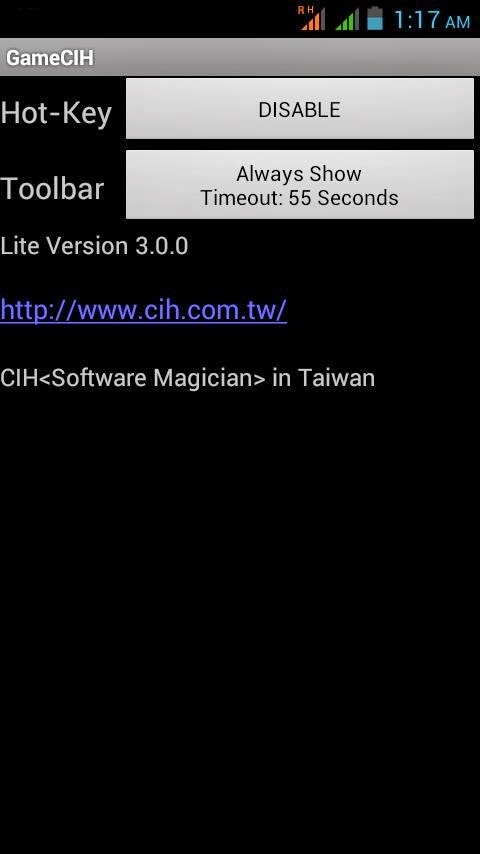
Step 1. First of all after rooting your android device open the GameCIH App. It will ask you for superuser access, grant it.(This will only come if you have properly rooted your android device. Now on the home screen of this app, you will see Hot-Key option, select any of them which you feel more convenient while using in your android.
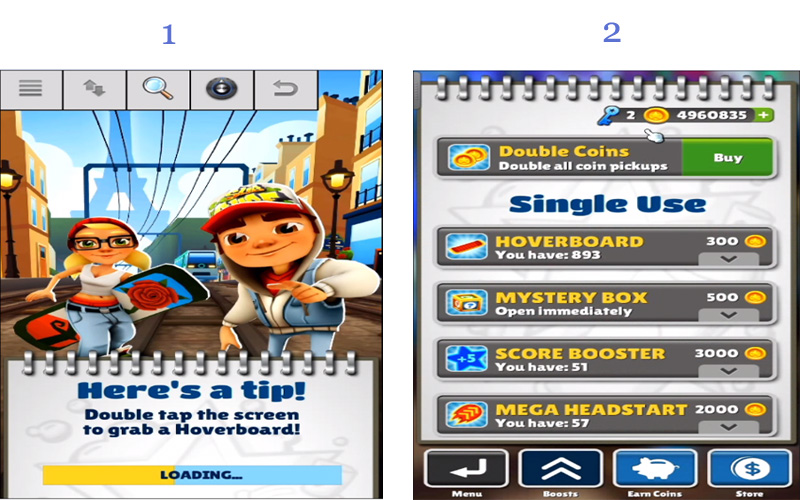
Step 2. Now open the game that you want to hack into your android device. Now pause the game and access the hotkeys displaying there, select any value that you want to edit in your game. Like any of text value like keys of subway surfer game.
Step 3. Enter your desired value in the text field box appeared there and click on done. Now you will see default value will get replaced with your value. Similarly, you can alter any values in any of the game according to your wish.
That's it game hacking is done, Now you can access any resources using this hack.
So above is all about Hack Any Game On Android. With the help of this trick, you can alter any coins, lives, money, weapons power and lots more in any of your favorite android game and can enjoy the unlimited game resources according to your wish.
Using Game Guardian
Game Guardian Apk is one of the best apps which you can have on your Android smartphone. With the help of this app, you can easily get unlimited coins, gems and can perform all other hacks. However, Game Guardian Apk needs a rooted Android smartphone to work. Here's a simple guide that will help you.
Step 1. First of all, you need to download the latest version of Game Guardian on your Android smartphone from the given download link above or below.
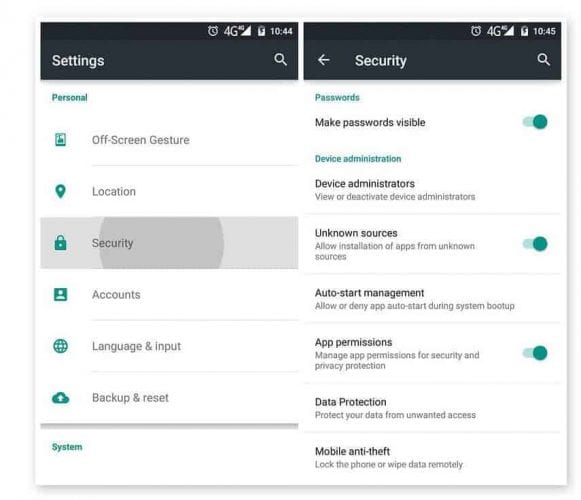
Step 2. After downloading on your smartphone, you need to enable the Unknown Source on your device. For that, you need to visit Settings > Security > Unknown Sources
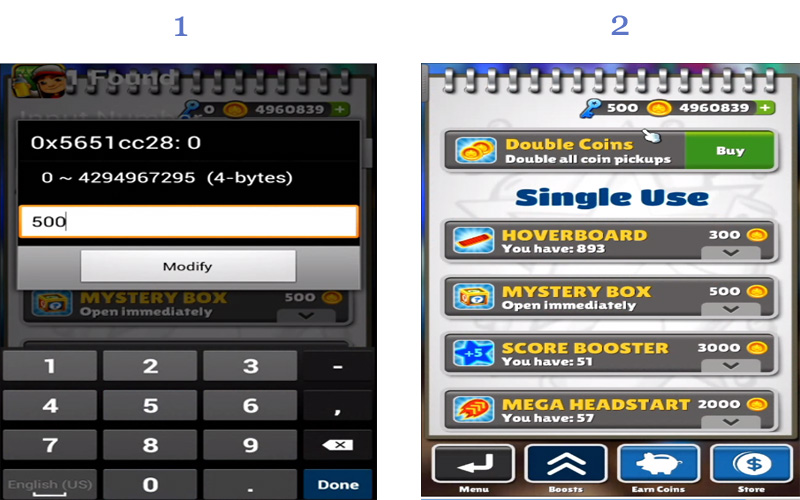
Step 3. Now install the app and then press the home button to minimize the app. Now open any game that you want to hack. You will see an overlay of Game Guardian App icon. Tap on it.
Step 4. Now you need to tap on the Search Button and set the value. If you don't know the values, then simply set it to auto.
Step 5. You need to search for the value which you want to hack like money, gem, health, score etc. You can change all those values. Suppose, if you need to decrease the number of values, you need to scan again for the new value.
Step 6. Finally, you need to select all the values and then change it to infinite numbers like '9999999' or whatever you want.
That's it, you are done! This is how you can use Game Guardian Apk to hack games on your Android smartphone.
With this, you can play a game at any levels without any shortage of any resource that can interrupt your gameplay. Hope you like this coolest android game hack. Don't forget to share it with others too.
Related articles
- Android Hack Tools Github
- Hacker Hardware Tools
- Hacking Tools Hardware
- Pentest Reporting Tools
- Game Hacking
- Hacking Tools Mac
- Hacking Tools For Games
- Hack Tool Apk No Root
- Kik Hack Tools
- Pentest Tools Download
- Hack Tools 2019
- Hacker Tools Hardware
- Pentest Tools Android
- Hack Tools Pc
- Hack Tools Github
- Hack Tools 2019
- Nsa Hack Tools
- Pentest Tools Linux
- Hack App
- Pentest Tools For Ubuntu
- Hack Tools 2019
- Hacking Tools Free Download
- Pentest Tools List
- Hacking Tools Usb
- Hackrf Tools
- Top Pentest Tools
- Pentest Tools Windows
- Pentest Tools Open Source
- Hack Website Online Tool
- Hacking Tools Kit
- Pentest Automation Tools
- Hacker Tools Mac
- Pentest Tools Online
- Pentest Tools Alternative
- Hack Tools For Mac
- Pentest Tools Bluekeep
- Hacking Tools
- Github Hacking Tools
- Tools Used For Hacking
- Pentest Tools Windows
- Hacker Tools For Windows
- Hack Tools
- Hack Tools For Games
- Best Pentesting Tools 2018
- Hack Tools Github
- Pentest Tools Website Vulnerability
- Hack Tools For Ubuntu
- Nsa Hack Tools Download
- Hack Tools For Windows
- Nsa Hack Tools Download
- Tools For Hacker
- Kik Hack Tools
- Physical Pentest Tools
- Pentest Tools Github
- Tools 4 Hack
- Kik Hack Tools
- Nsa Hacker Tools
- Hacking Tools Mac
- Hacking Tools For Windows
- Pentest Tools Url Fuzzer
- How To Install Pentest Tools In Ubuntu
- Hacker Tools Apk
- Hacking Apps
- Hacking Tools For Windows Free Download
- Hacker Tools For Windows
- Hacker Tools Hardware
- Github Hacking Tools
- Pentest Tools Framework
- Pentest Tools Linux
- Hacker Tools
- Hacker Tools 2020
- Hacking Tools And Software
- Nsa Hack Tools Download
- Pentest Tools List
- Pentest Tools For Mac
- Hacking Tools Hardware
- Blackhat Hacker Tools
- Hacker Hardware Tools
- Pentest Tools Alternative
- Hack Tools For Ubuntu
- Android Hack Tools Github
- Hacking Tools Github
- What Are Hacking Tools
- Hack Apps
- Black Hat Hacker Tools
- Free Pentest Tools For Windows
- Hacker Tools For Windows
- Hack Tools Github
- Bluetooth Hacking Tools Kali
- Pentest Tools For Windows
- Hack Tools
- Hacking Tools 2019
- Pentest Tools Kali Linux
- Pentest Tools Open Source
- Hacking Tools For Kali Linux
- Blackhat Hacker Tools
- Bluetooth Hacking Tools Kali
- Hacker Tools Free
- Black Hat Hacker Tools
- Hacker Security Tools
- Hack Tools For Pc
- Pentest Tools Github
- Hacker Tool Kit
- Game Hacking
- Hack And Tools
- Hacking Tools Windows
- Hack Tool Apk No Root
- Physical Pentest Tools
- Pentest Tools Github
- Pentest Tools Find Subdomains
- Nsa Hack Tools Download
- What Are Hacking Tools
- Hacker Tools Free
- Hacker Tools For Windows
- Hacking Tools 2019
- Hacker Hardware Tools
- Pentest Tools Framework
- Termux Hacking Tools 2019
- Pentest Automation Tools
- Hacking App
- Hacking Tools Download
- Hacker Tools Software
- Hacking Tools Windows
- Hackers Toolbox
- Free Pentest Tools For Windows
- Pentest Tools Github
- Pentest Box Tools Download
- Pentest Tools Download
- Hacker Tools Apk
- Pentest Tools Nmap
- Install Pentest Tools Ubuntu
- Hacking Apps
- Pentest Tools Website
- Bluetooth Hacking Tools Kali
- Hack App
- World No 1 Hacker Software
- Hackrf Tools
- Hacker Tools Linux
- Pentest Tools Download
- How To Hack
- Pentest Tools Github
- Pentest Tools For Mac
- Hacking Tools For Windows
- Hacker Tools